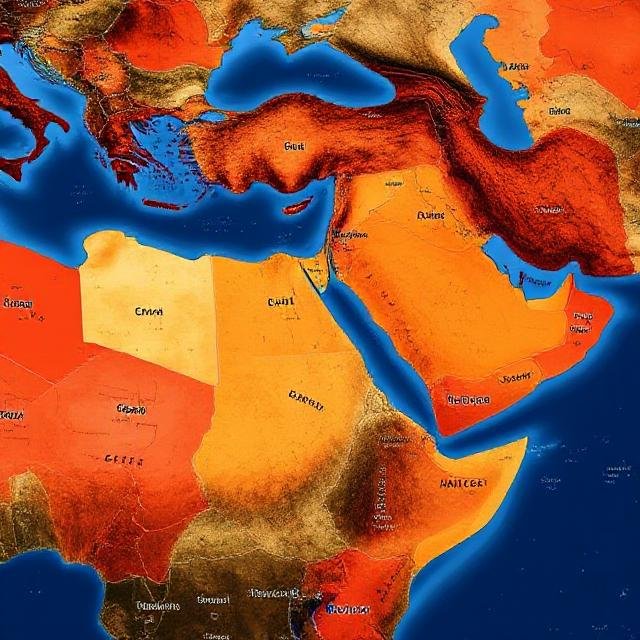
Desert Dexter's AsyncRAT Campaign Targets Middle East and North Africa
A new cyber campaign deploying a modified version of the AsyncRAT malware has been targeting users across the Middle East and North Africa (MENA) region since September 2024, with attackers leveraging social media platforms for distribution.
A new cyber campaign deploying a modified version of the AsyncRAT malware has been targeting users across the Middle East and North Africa (MENA) region since September 2024, with attackers leveraging social media platforms for distribution.
According to researchers Klimentiy Galkin and Stanislav Pyzhov from Positive Technologies, the operation exploits the current geopolitical climate by spreading malware via legitimate online file-sharing platforms and Telegram channels specifically created for this purpose. Their findings, published last week, indicate that the campaign has infected approximately 900 victims across Libya, Saudi Arabia, Egypt, Turkey, the United Arab Emirates, Qatar, and Tunisia since its emergence in fall 2024.
Attack Strategy and Infection Chain
Attributed to a threat actor named Desert Dexter, the campaign was uncovered in February 2025. The attackers primarily create temporary Facebook accounts and news channels, using them to share advertisements containing links that lead to file-sharing services or Telegram channels hosting the malware.
Once a user clicks on the link, they are led to a modified version of AsyncRAT, which has been altered to:
- Include an offline keylogger
- Search for 16 cryptocurrency wallet extensions and applications
- Communicate with a Telegram bot
The infection process begins when the victim downloads a RAR archive containing either a batch script or a JavaScript file, both of which execute a PowerShell script to initiate the second stage of the attack.
The PowerShell script:
- Terminates .NET-related processes that could interfere with the malware's execution
- Deletes script files (BAT, PS1, and VBS) from specific directories
- Creates new script files in the C:\ProgramData\WindowsHost and C:\Users\Public folders
- Establishes persistence, gathers system information, captures screenshots, and sends data to a Telegram bot
- Injects the AsyncRAT payload into the aspnet_compiler.exe process
Attribution and Possible Origin
The identity of the attackers remains unknown, though Arabic-language comments embedded in the JavaScript file suggest a regional origin.
Further investigation of the Telegram bot communications linked to the malware revealed screenshots from the attacker's own desktop, which contained:
- A PowerShell script
- A tool named Luminosity Link RAT
- A desktop folder named "DEXTERMSI"
- A link to a Telegram channel named "dexterlyly", created on October 5, 2024, possibly indicating a Libyan connection
Targeted Sectors and Impact
Most victims appear to be regular users, including employees in industries such as:
- Oil production
- Construction
- Information technology
- Agriculture
Despite using relatively simple tools, Desert Dexter has managed to infect a significant number of devices by combining Facebook ads, legitimate hosting services, and references to current geopolitical events, the researchers noted.
Global Cyber Threat Landscape
Meanwhile, cybersecurity firm QiAnXin has exposed details of Operation Sea Elephant, a separate spear-phishing campaign targeting scientific research institutions in China. This operation, attributed to a group labeled UTG-Q-011, focuses on delivering a backdoor designed to collect sensitive data related to ocean sciences and technologies.
UTG-Q-011 is believed to be a subset of a larger adversary collective known as the CNC group, which shares tactical similarities with Patchwork, a suspected Indian threat actor.














