RansomHub’s EDRKillShifter Tool Links Affiliates to Medusa, BianLian, and Play Ransomware
A recent analysis has revealed connections between RansomHub affiliates and other ransomware groups such as Medusa, BianLian, and Play, highlighting shared tools and tactics among these threat actors.
Shared EDR-Killing Tool Unveils Overlapping Ransomware Operations
A recent analysis has revealed connections between RansomHub affiliates and other ransomware groups such as Medusa, BianLian, and Play, highlighting shared tools and tactics among these threat actors.
Common EDR-Killing Tactic Connects Ransomware Groups
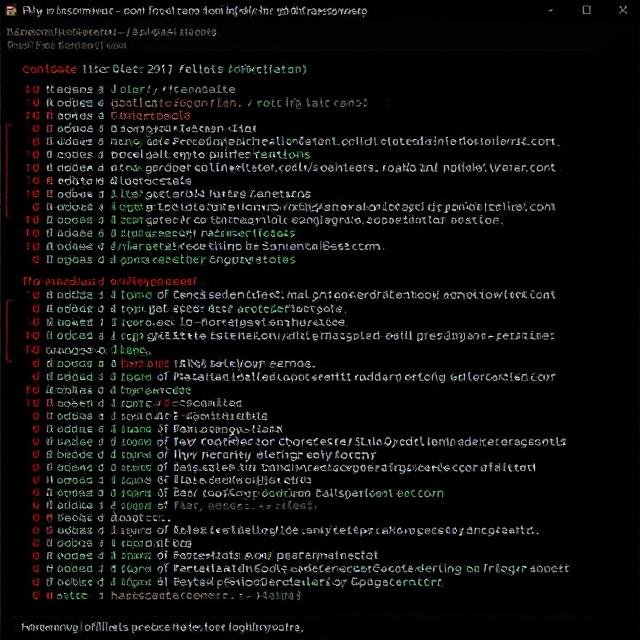
The key link between these ransomware operations is the use of EDRKillShifter, a custom-built tool designed to disable endpoint detection and response (EDR) solutions on compromised systems. This tool, first associated with RansomHub in August 2024, leverages a well-known Bring Your Own Vulnerable Driver (BYOVD) technique to bypass security defenses and enable seamless ransomware deployment.
According to ESET researchers Jakub Souček and Jan Holman, ransomware affiliates rely on such tools because updating ransomware encryptors too frequently increases the risk of introducing flaws. Instead, they focus on deploying EDR killers to neutralize security measures before launching the encryption process.
Affiliates of Multiple Ransomware Groups Share RansomHub’s Tool
What makes this discovery significant is that EDRKillShifter was specifically developed by RansomHub’s operators and distributed among its affiliates. However, researchers found the same tool being used in ransomware attacks linked to Medusa, BianLian, and Play—despite the fact that Play and BianLian traditionally operate under a closed Ransomware-as-a-Service (RaaS) model, where they only work with trusted, long-term affiliates.
ESET suggests that trusted members of Play and BianLian have collaborated with RansomHub affiliates and then repurposed RansomHub’s EDRKillShifter tool for their own attacks. This is unusual, as closed ransomware groups typically stick to a consistent set of tools rather than incorporating tools from external actors.
The findings also point to a possible shared threat actor, codenamed "QuadSwitcher," who appears to have the strongest ties to Play, based on similarities in attack techniques.
Rise in BYOVD-Based EDR Killers
RansomHub’s EDRKillShifter is not the only EDR-killing tool making headlines. Another affiliate, CosmicBeetle, has deployed EDRKillShifter in RansomHub and fake LockBit attacks. Similarly, the Embargo ransomware gang was found using MS4Killer to disable security software in 2024, and the Medusa ransomware group recently adopted a custom malicious driver dubbed ABYSSWORKER.
Mitigation Strategies
Security experts stress the importance of detecting and mitigating threats before attackers gain administrative privileges. Organizations should:
-
Enable detection of potentially unsafe applications to block the installation of vulnerable drivers.
-
Monitor for early signs of intrusion, as deploying an EDR killer requires admin-level access.
-
Implement strict security policies to prevent attackers from exploiting weak points in endpoint defenses.
As ransomware operations continue to evolve and collaborate, defenders must stay ahead by strengthening endpoint security and monitoring for emerging threats.














